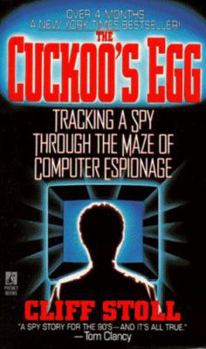
The Cuckoo's Egg: Tracking a Spy Through the Maze of Computer Espionage
Select Format
Select Condition 
Book Overview
In this white-knuckled true story that is "as exciting as any action novel" (The New York Times Book Review), an astronomer-turned-cyber-detective begins a personal quest to expose a hidden network of... This description may be from another edition of this product.
Format:Mass Market Paperback
Language:English
ISBN:0671726889
ISBN13:9780671726881
Release Date:November 1990
Publisher:Pocket Books
Length:356 Pages
Weight:0.43 lbs.
Dimensions:1.0" x 4.2" x 6.7"
Customer Reviews
5 ratings
Appropriately named.
Published by bernie4444 , 28 days ago
A cuckoo bird will lay its egg in another bird's nest, letting that bird raise the offspring as its own.
I saw the TV program on this story before reading the book. Coming from a UNIX background, it was fun to see a system I recognized. It could have been titled "The Story of Ping." Oops, that title has been taken. I remember being billed for time on the computer, and I could only gain access at 2 AM. Many of these skills are now lost to people who do not have a shell account. I especially like how they kept the intruder on the line long enough to track. The hunt was intriguing, and it makes you wonder what is happening today. While this book deals with such things as passwords, the many new avenues created on today's Internet may afford a newer mystery. Until then, this is the classic.
A student managing the computer at Berkley notices an unusual charge to his account. He finds that someone is hacking before it is fashionable. To track down the culprit(s), he must first learn the tracking skills. This process is in its infancy, so he even has to invent a few of the skills himself. The use of timing and knowledge of the speed of light allows a good estimate of the distance. The only way to go through the old timing switching stations was to hold the intruder online long enough. This required creating a dummy database with intriguing information.
Who are these mysterious intruders?
Will they get caught?
What implications does it hold for us today?
The best spy story, and you'll love the author
Published by Claude Lambert , 2 years ago
When the internet as we know in was born, in 1983, it was perfectly innocent: a way for scientists to communicate with each other in a spirit of trust. The idea that some people would use it to steal your money or government secrets was just inconceivable. But it did not last long!
In 1986, Cliff Stoll was a young astronomer making a living as systems administrator at Berkeley Laboratory. He was charged with finding why there was a 75 cents error in the account of computer time. It is a ridiculous question, but scientists are all the same, it there is something they don't understand, no matter how trivial, they will munch, chew and bite it until they get the answer. And what did Cliff find? He found a spy. Even the FBI was stunned. This is an exciting book about new ways to commit crimes. Yes, technology has changed since then, what does not change is us, humans, the good and the bad ones. A pleasure to read.
The unintentional counterespionage agent
Published by Thriftbooks.com User , 23 years ago
_The Cuckoo's Egg_ has everything most fictional detective novels wish that they had: a personable detective who does not mean to get involved as deeply as he does, federal agencies who cannot seem to take action, and a criminal mastermind who has everybody stumped until he encounters our detective. The best part of this whole book is that it really happened-- a feat that fictional mysteries can never match. I knew Stoll's work through the more technical article "Stalking the Wily Hacker" and was pleasantly surprised to see how well Stoll was able to translate the technical side into a book-length narrative. IMO, this is significantly better than other more recent books about computer crime and still worth a read today (both for information and entertainment). Highly recommended.
Now it's time for the Hunter to become the hunted!
Published by Thriftbooks.com User , 26 years ago
This was the second computer security book I read and it was like adding flame to a fire because it increased my curiosity and prompted me to want to know more about it, so I ended up reading Cyberpunk by Katie Hafner and John Markoff to get a more inside look. If you start reading it then you'll probably finish it the same day. It talks a scientist that stumbles on a mistake in the accounting part of his job as a scientist at Lawrence Berkely Lab and he makes the mistake into a chase through cyberspace. In the book the author takes on the role as a modern day Sherlock Holmes and in the end he realizes that it was only elementary.Dealing with the CCC (Chaos Computer Club), Hunter (the main hacker), and the different networks will really make you think and keep you on your toes. Read it and see for yourself just how intense the experience will be. I advise you to get some sleep before you start because you probably won't be getting any anytime soon.
Excellent book.
Published by Thriftbooks.com User , 28 years ago
This book suceeds on many levels. Its a well written suspenseful spy novel that evolves very smoothly and engages the reader very early on. It is also an excellent description of computer / telecommunications technology that most anyone can understand, since he goes to the trouble to stop and explain, in laymens terms, UNIX utilities, daemon outputs, satellite technology, and microwave-oven protocol (check out the sneaker-melting fiasco on p 269). Stoll proves to be hell-bent on capturing the rogue user despite the lack of support from superiors and government agencies, and the toll it takes on his personal life. His frustrated accounts of his treatment at the hands of federal agencies as he petitions assistance from the FBI, the CIA, the NSA (among others) in capturing this potentially dangerous mole are testaments to the power of beaucracy in this country. However, he still manages to humanize the employees of these otherwise caricatured federal agencies by describing them as real people who want to help, rather than just surly trench-coated spies. I especially enjoyed reading about Stoll's low-tech solutions to slowing the hacker as he rifled through delicate documents by jangling keys over the connector to resemble static (simply cutting the line would have tipped the hacker off). This is a very enjoyable book, and I'd also recommend the reader try to find a videocassette copy of the NOVA TV special on PBS. Although it loses a lot of the book's details in the attempt to condense into one hour, it allows the viewer to see and hear the author, one of the quirkiest, most entertaining techno-goobers you'll come across.